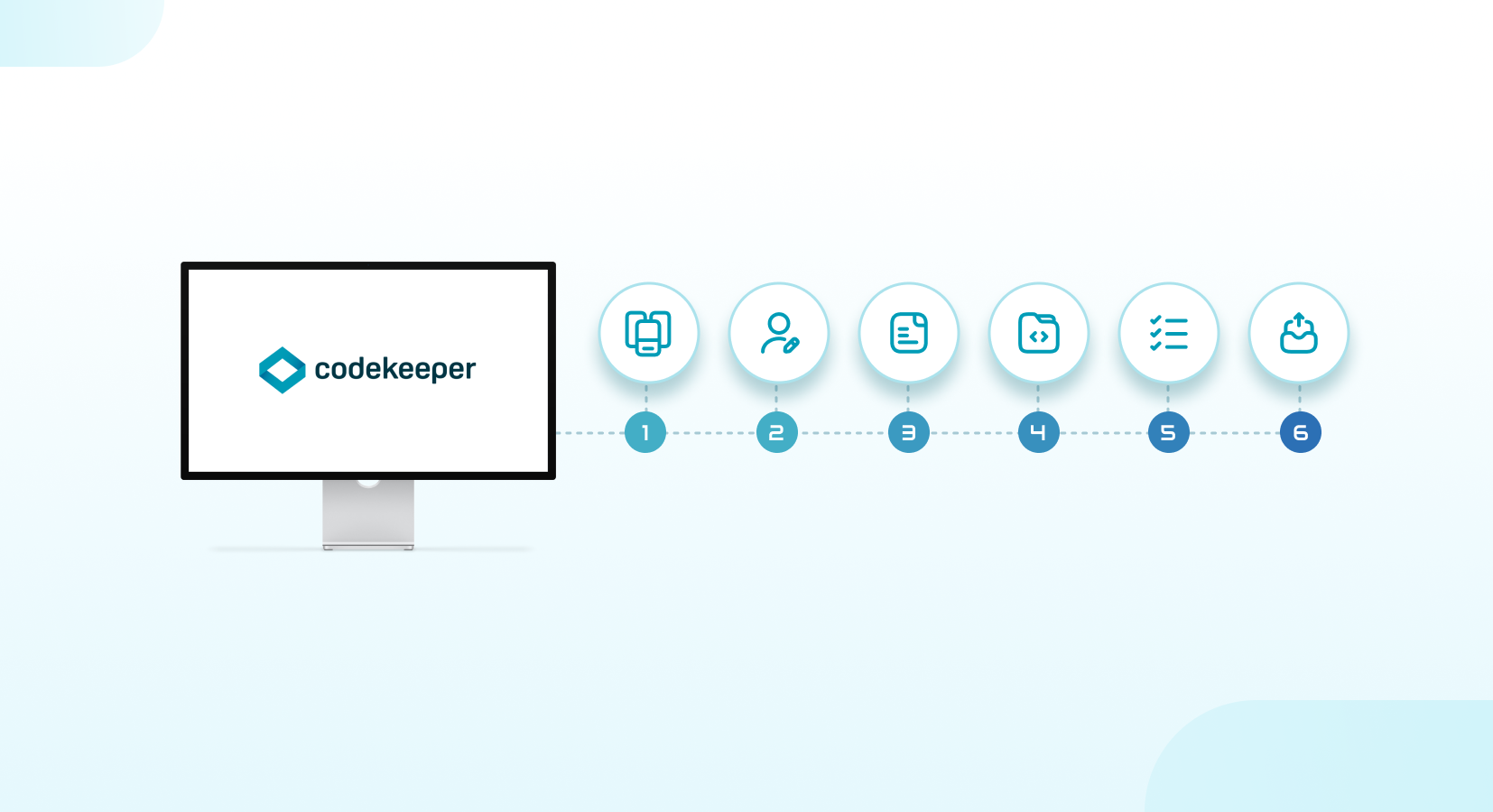
Setting up a source code escrow account with Codekeeper is a straightforward process that can provide peace of mind for both software vendors and their clients. By using Codekeeper's software escrow services, you can ensure that critical information is stored securely and released in the event of an unexpected situation.
source code escrow, software escrow, software escrow agreements, codekeeper
source code escrow, software escrow, software escrow agreements, codekeeper
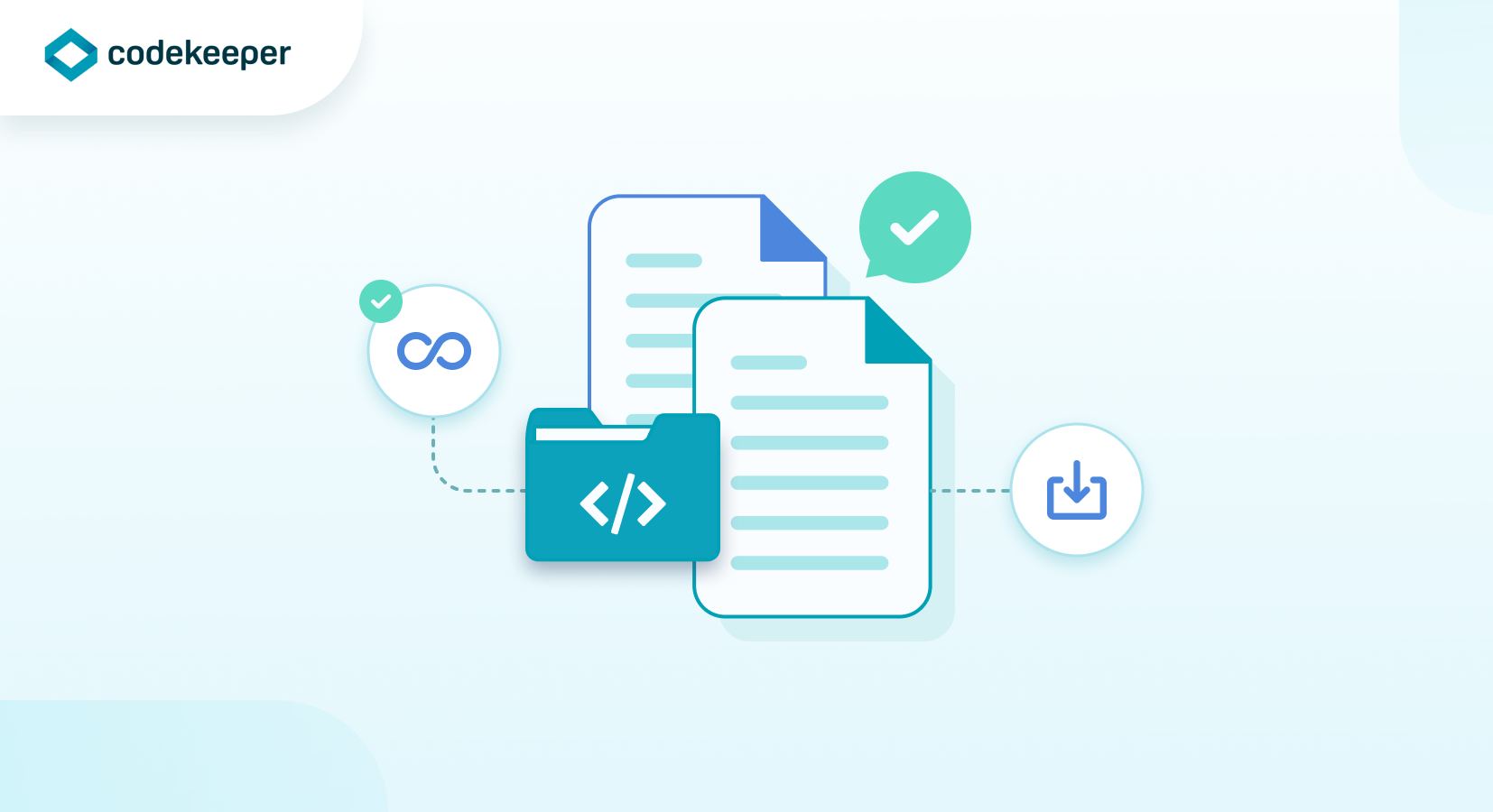
Software escrow is a service that provides storage and release of source code and other critical information for software products with a neutral third party like Codekeeper. In the event of an unexpected situation, such as a software vendor going out of business or failing to provide support, software escrow can be a valuable tool for ensuring business continuity and minimizing risk.
There are many benefits of software escrow for both software vendors and their clients. In this article, we will discuss some of the key benefits of software escrow and how it can help organizations like yours protect their investments in software products.
Business Continuity
One of the most significant benefits of software escrow is business continuity. If a software vendor goes out of business or fails to provide support for their software product, clients who have invested in that software may be left without access to critical source code and other information needed to maintain and support the software.
With software escrow, clients can ensure that they have access to critical information even if the software vendor is no longer available. This means that they can continue to use and support the software without interruption, minimizing the risk of business disruption and loss of revenue.
Risk Management
Software escrow is also an effective risk management tool. By storing critical information with a software escrow agent like Codekeeper, software vendors can reduce the risk of information loss or theft. This is particularly important in industries where intellectual property is a key asset, such as software development.
Clients who invest in software products also benefit from reduced risk through software escrow. By ensuring that they have access to critical information, clients can minimize the risk of software failure or data loss, which can have serious consequences for their business.
source code escrow, software escrow, saas escrow, codekeeper, operational resilience
In today's digital age, security breaches and operational disruptions can have disastrous consequences for any business. From lost revenue to reputational damage, the impacts of such incidents can be long-lasting and far-reaching. Ensuring both security and operational resilience is therefore crucial for businesses of all sizes and industries. In this article, we will discuss some best practices for ensuring security and operational resilience in your organization.
Develop a Security and Resilience Strategy
A well-defined security and resilience strategy is the foundation of any successful program. Such a strategy should take into account the unique risks and challenges faced by your organization, as well as any relevant regulations or compliance requirements. Key components of a security and resilience strategy include:
Risk Assessment : Identify and assess the risks to your organization's security and operations. This can include internal and external threats, as well as vulnerabilities in your systems, processes, and personnel.Incident Response Plan : Develop a plan for responding to security incidents and operational disruptions. This should include procedures for detecting, containing, and mitigating the impact of incidents, as well as for communicating with stakeholders.
Business Continuity Plan : Develop a plan for maintaining critical business operations in the event of a disruption. This should include procedures for backing up data and systems, as well as for restoring operations as quickly as possible. This can be achieved by way of investing in software escrow, for example.
Training and Awareness : Ensure that all employees are aware of the risks and procedures related to security and resilience. Regular training and awareness programs can help to reduce the risk of human error and improve incident response times.
Implement Strong Access Controls
Access controls are essential for protecting sensitive data and systems from unauthorized access. This includes both physical and digital access controls. Key considerations for implementing strong access controls include:
Role-Based Access : Assign access levels based on an individual's job responsibilities and need-to-know. This can help to limit the exposure of sensitive information to those who do not require access.Multi-Factor Authentication : Use multiple authentication factors, such as passwords and biometric data, to increase the security of access controls. This can help to reduce the risk of unauthorized access due to lost or stolen credentials.
Regular Reviews : Conduct regular reviews of access controls to ensure that they remain appropriate for each individual's job responsibilities. This can help to prevent access creep, where individuals accumulate unnecessary access over time.
Use Encryption to Protect Data
Encryption is a key tool for protecting sensitive data from unauthorized access. It involves the conversion of data into a format that can only be read by those who have the appropriate decryption key. Key considerations for using encryption to protect data include:
Choosing the Right Algorithm : Select an encryption algorithm that is appropriate for the level of security required for each type of data. This can include symmetric and asymmetric encryption, as well as hashing algorithms for data integrity.Key Management : Develop a key management strategy that ensures that encryption keys are properly secured and only accessible to authorized personnel. This can include using hardware security modules (HSMs) and key rotation policies.
End-to-End Encryption : Implement end-to-end encryption for all sensitive data in transit and at rest. This can help to prevent data breaches and unauthorized access to sensitive information. At Codekeeper, all the data you store with us is end-to-end encrypted for example.
source code escrow, software escrow, saas escrow, codekeeper
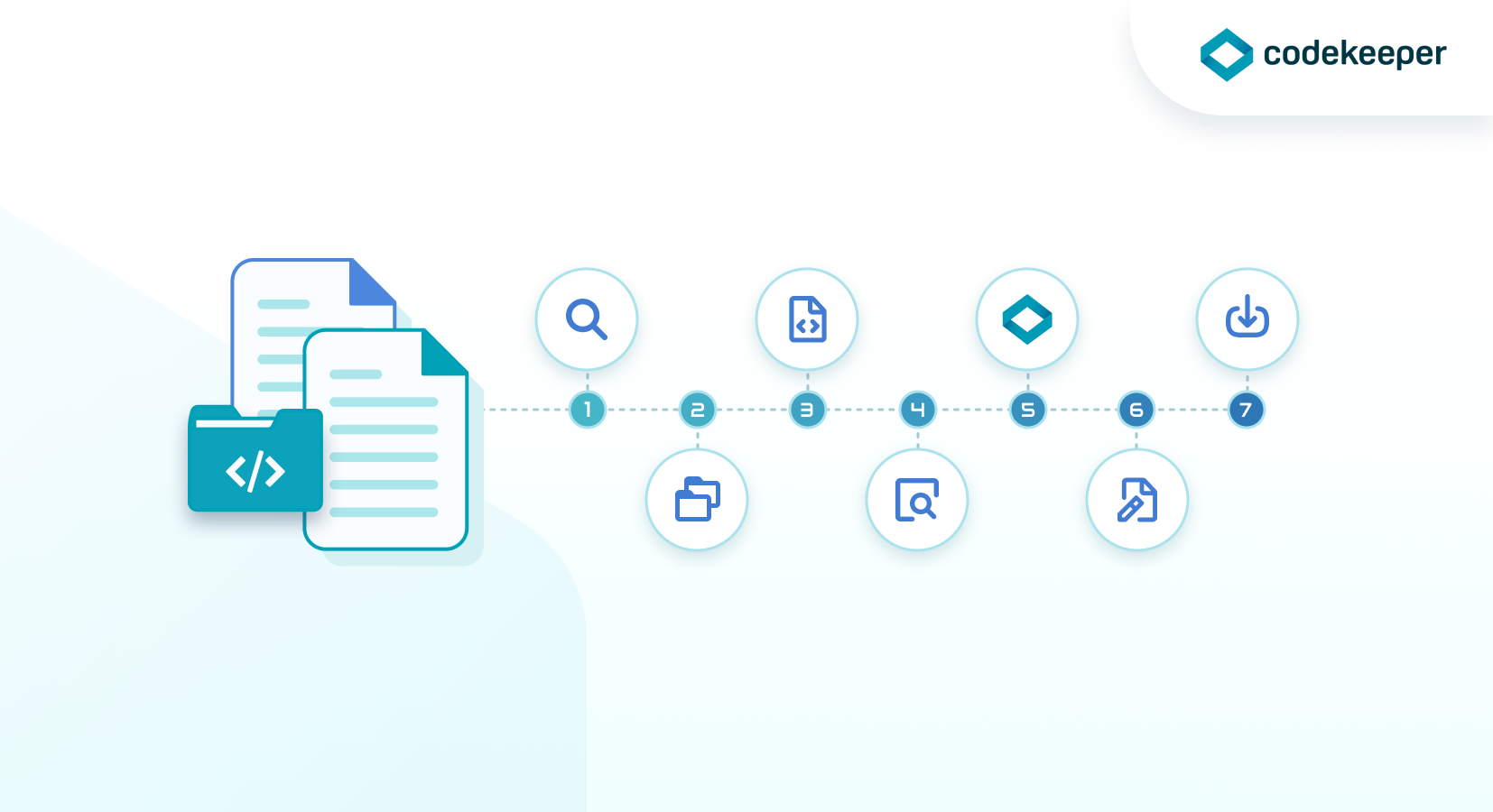
The protection of digital assets is more critical than ever, and one way to ensure the security of your source code is by using software escrow services. In this article, we will discuss what software escrow is, why you need it, and how it works.
What is Software Escrow?
Software escrow is a legal agreement between three parties: the software owner or licensor, the end-user or licensee, and a third-party escrow agent like Codekeeper. The agreement states that the software owner deposits the source code and other critical materials with us as a neutral third party. In the event that the software owner is unable to support the software due to circumstances ranging from bankruptcy, acquisition, natural disasters, etc., the end user/beneficiary can access the deposited materials.
Why Do You Need Software Escrow?
As a software owner or licensor, you invest significant time and resources in developing your software. It goes without saying that the protection of your intellectual property is critical to your success. There are several reasons why you may need software escrow:
- Protect Your Intellectual Property: When you deposit your source code with Codekeeper, you retain ownership of the intellectual property. This ensures that your source code remains secure and accessible in the event of unforeseen circumstances.
- Reduce Risk: By using software escrow services, you can reduce the risk of your end-users experiencing downtime or other issues due to your inability to support the software. This can help you maintain customer loyalty and avoid legal disputes.
- Increase Customer Confidence: Providing software escrow services to your end-users demonstrates your commitment to customer satisfaction and can help you win new business.
- Comply with Regulations: In some industries, such as healthcare and finance, regulations require the use of software escrow services to protect patient and customer data. We provide GDPR and HIPAA compliance solutions.
software escrow, codekeeper, software escrow agent
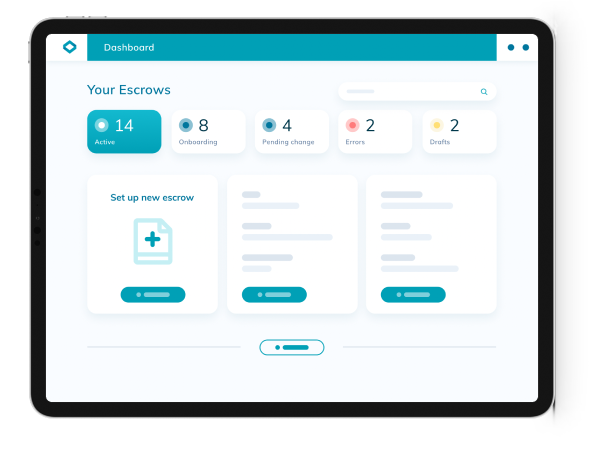
After months of sleepless nights filled with seemingly endless coding and testing, it is finally here. We’re excited to introduce you to the all-new Codekeeper V4!
software escrow, codekeeper, software escrow agent
Software escrow is an important part of any software development project. It ensures that the software end-user has access to the source code in case of a dispute or other unforeseen circumstances like a natural disaster, or even death.